Beyond the Scan: What Is Penetration Testing, and Why Your Organization Needs It Now
Most organisations run vulnerability scans.
Far fewer truly understand how an attacker would move through their environment.
That distinction matters.
In today's threat landscape, identifying weaknesses is no longer enough. Security leaders need to understand which issues are actually exploitable, which control failures can be chained together, and what those attack paths mean for business risk, resilience, and response readiness.
That is the role of penetration testing.
Penetration testing goes beyond surface-level detection. It helps organisations validate whether their security controls work in practice, uncover realistic attack paths, and measure how prepared they are when prevention fails.
In other words, vulnerability scanning tells you what may be wrong. Penetration testing tells you what an attacker can actually do with it.
The difference between vulnerability scanning and penetration testing
Vulnerability scanning is an important part of any security program. It provides broad visibility across known weaknesses such as missing patches, outdated components, insecure configurations, exposed services, and common misconfigurations.
It is:
- Fast.
- Scalable.
- Necessary.
But it is not the same as penetration testing.
A vulnerability scanner does not think like an attacker. It does not usually determine whether multiple weaknesses can be chained together. It does not validate business impact in a realistic way. And it does not answer the questions security leaders often care about most:
- Can this issue actually be exploited in our environment?
- Does it lead to privilege escalation, lateral movement, or data exposure?
- Would our controls stop a determined attacker?
- Would our team detect and respond effectively?
Penetration testing answers those questions.
It replaces assumption with evidence.
Why organisations need more than automated scanning
Modern environments are dynamic.
Cloud infrastructure changes continuously. Development pipelines evolve with every release. Identities, permissions, integrations, and dependencies shift faster than traditional assurance models can keep up.
As a result, many organisations have strong-looking security dashboards but limited confidence in how their environment would behave under real attack conditions.
This is where automated scanning reaches its limit:
- A scanner may tell you that an issue exists.
- A penetration test shows whether that issue matters.
For example, a single exposed secret may appear isolated in a scan result. In practice, that secret may unlock a CI/CD pipeline, grant access to a cloud role, or create a path to sensitive production-adjacent systems. A weak authorisation flaw may look low-risk until it is combined with predictable object references and poor role boundaries. An internal service exposure may appear minor until it enables lateral movement.
Attackers do not think in isolated findings:
- They think in paths.
Penetration testing helps organisations see those paths before adversaries do.
What real penetration testing delivers
A mature penetration testing program does more than produce a report. It delivers operational clarity.
1. Validation of security controls
Many organisations invest heavily in security controls without fully validating how those controls perform under realistic attack conditions.
They may have MFA, WAFs, IAM guardrails, endpoint controls, pipeline protections, logging platforms, and detection content in place. But until those controls are challenged through adversarial testing, leadership is often relying on design assumptions rather than proven outcomes.
Penetration testing validates whether your controls work as intended in the real world:
- Not whether they exist.
- Whether they hold.
2. Discovery of exploitable attack paths
One of the most valuable outcomes of penetration testing is the identification of attack paths that would never be visible through isolated scanning alone.
Security incidents rarely result from one issue in isolation. They are more often the product of weak trust boundaries, excessive permissions, exposed secrets, poor input handling, misconfigured workflows, and control gaps that can be chained together.
Penetration testing reveals those chains.
It shows how an attacker could move from initial access to meaningful impact.
3. Improved incident readiness
Penetration testing is also a readiness exercise.
It helps organisations evaluate whether they would actually detect malicious activity, whether logs and telemetry are sufficient, whether escalation paths are clear, and whether responders understand the likely blast radius of compromise.
This is especially important for modern enterprises operating across cloud, SaaS, identity, and software delivery ecosystems. It is no longer enough to ask whether an issue exists. Organisations must ask whether they are ready when exploitation happens.
The limitations of traditional pentesting
Traditional penetration testing remains valuable, but many legacy approaches are too periodic for modern attack surfaces.
A once-a-year assessment cannot fully reflect an environment that changes every week.
- Applications change.
- Pipelines change.
- Identities change.
- Dependencies change.
- Attack techniques change.
That is why many organisations are moving toward a more continuous model of adversarial validation - one that complements periodic expert-led testing with repeatable, evidence-backed workflows.
The future of penetration testing is not just manual or automated.
It is structured, continuous, and intelligence-driven.
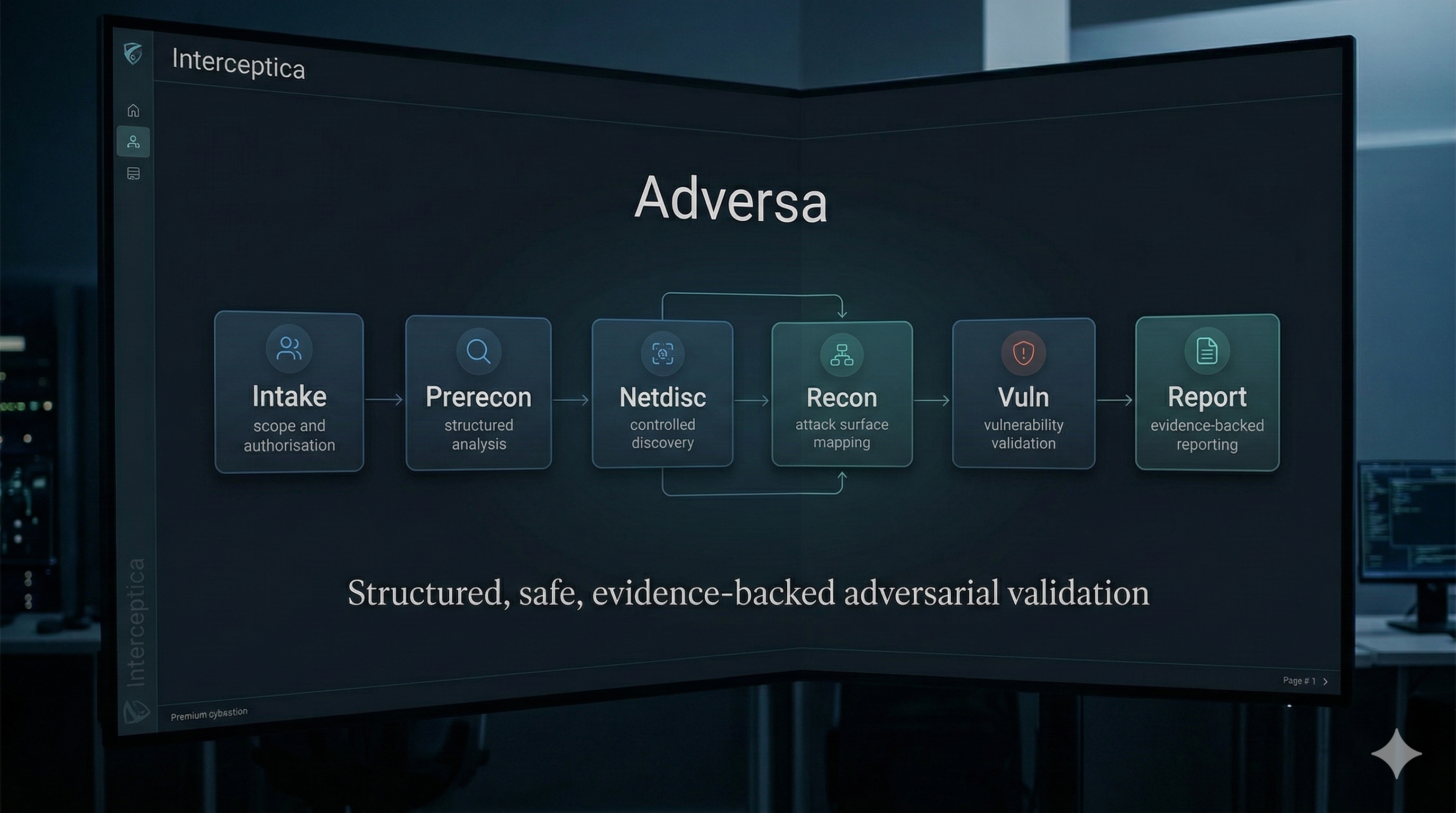
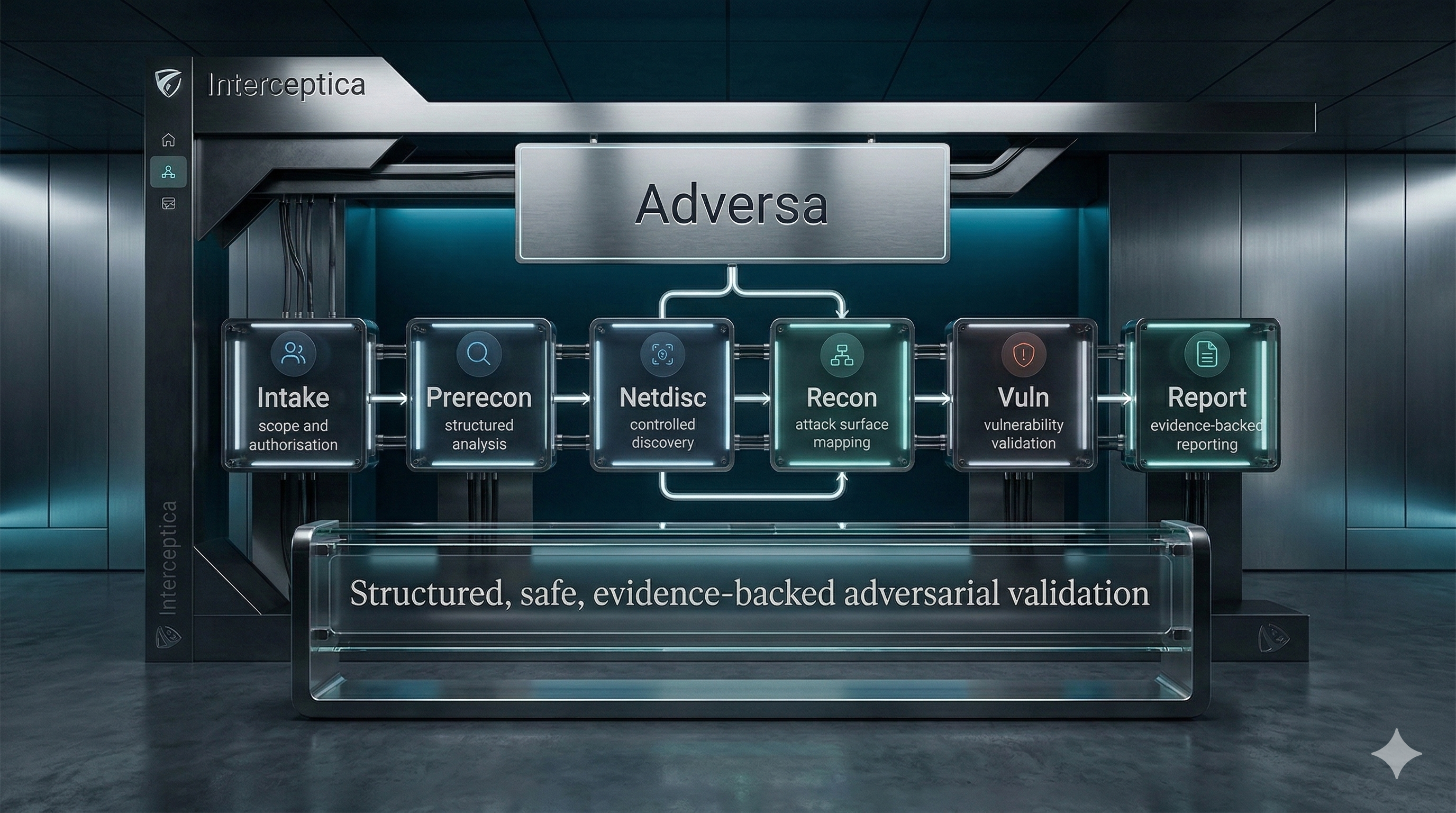
Where Adversa fits
At Interceptica, we believe the next evolution of offensive security must combine real attacker thinking, strong safety controls, and evidence-backed outputs.
That is the philosophy behind Adversa.
Adversa is designed to help organisations move beyond fragmented testing and toward a more repeatable, structured model of penetration testing and adversarial validation.
Its value is not in generating noise. Its value is in helping security teams understand attack paths, validate assumptions, and produce clear, defensible security evidence.
That is increasingly important in an era where offensive security automation must also be safe, governed, and enterprise-ready.
For each stakeholder, the outcome is clear:
- For security leaders, that means greater confidence.
- For engineering teams, that means clearer remediation priorities.
- For the organisation, that means better security decisions grounded in real attack logic.
Beyond the scan means beyond isolated findings
This is the strategic shift many organisations now need to make.
Vulnerability scanning is foundational. It provides breadth.
Penetration testing provides depth.
- Scanning tells you what is present.
- Penetration testing tells you what is exploitable.
- Scanning identifies issues.
- Penetration testing validates impact.
- Scanning supports hygiene.
- Penetration testing supports resilience.
The strongest security programs need both.
But when leadership needs to understand real exposure, real attack paths, and real readiness, penetration testing becomes indispensable.
What a modern penetration testing program should look like
A modern penetration testing program should not be treated as a one-off compliance exercise.
It should function as part of a broader security validation strategy that includes:
- continuous visibility into weaknesses
- targeted adversarial testing of high-value systems
- attack-path based validation of risk
- evidence-backed reporting for remediation and retesting
- improved feedback loops between security, engineering, and leadership
This is how organisations move from reactive security to validated security.
Final thoughts
The organisations that will lead in the years ahead will not simply be the ones with more alerts, more tools, or more dashboards.
They will be the ones with greater clarity.
- Clarity on which weaknesses matter.
- Clarity on how attackers could move.
- Clarity on whether controls work.
- Clarity on how prepared the organisation is to respond.
That is what penetration testing provides.
It does not replace vulnerability scanning. It elevates it.
It turns raw findings into strategic understanding.
And that is exactly why organisations need it now.
How Interceptica helps
Interceptica helps organisations strengthen security through modern offensive security, attack-path validation, and continuous adversarial thinking.
If your organisation wants to move beyond surface-level findings and understand what is actually exploitable in your environment, Adversa is built to support that journey.
If this article reflects your reality, now is the right time to evaluate Adversa and move from periodic testing to continuous adversarial validation.
Adversa Enterprise is coming soon, bringing deeper governance, team workflows, and enterprise-scale operational control.
